HPKP has been deployed
It’s live, prepare to self-destruct in 3..2..1..
HTTP Public Key Pinning (HPKP)
A new HTTP header that allows web host operators to instruct user agents to remember (“pin”) the hosts’ cryptographic identities over a period of time. During that time, user agents (UAs) will require that the host presents a certificate chain including at least one Subject Public Key Info structure whose fingerprint matches one of the pinned fingerprints for that host. Source: RFC 7469
Why wold you consider HPKP?
To reduce the risk of Man-in-the-middle (MITM) attacks with forged certificates from a compromised or rogue CA. I initially believed HPKP would prevent HTTPS inspection but alas that’s not the case. Unfortunately browsers disables pinning for certificate chains with private root certificates, meaning this kind of “Kaspersky in the middle” crap is still approved. Yes… we should not break surveillance tools, that would be… bad?
What am I pinning?
I’m exclusively pinning on the leaf level (my own keys).
Public-Key-Pins: pin-sha256="+hReE4xfHXOZfSBOvDCmpORYCfn2VlYVMB4nRVUeLns="; pin-sha256="C8gw6A3tgLpxbpcE0J5rDd/P88yxiUhqUUalkGjTO8M="; max-age=2592000; includeSubDomains
I’m going to add a report-uri to receive validation failures in the future and I probably need a few more backup pins as well.
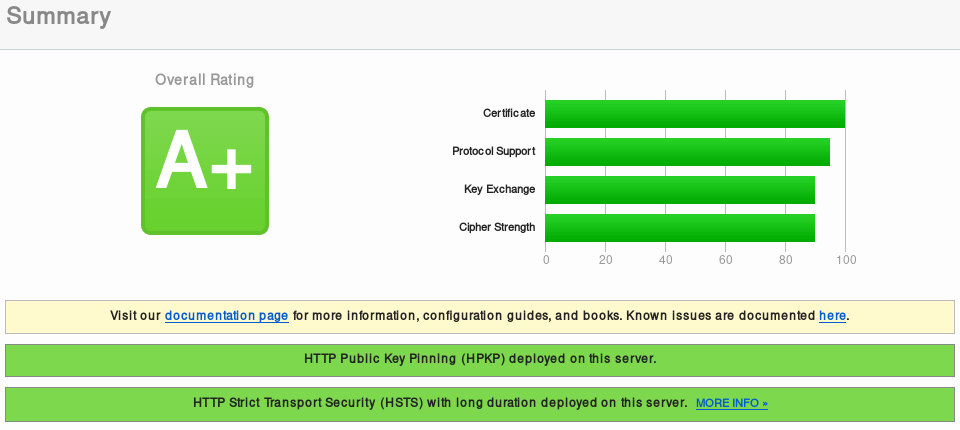
SSL report from ssllabs.com highlighting HPKP and HSTS.
Why are so few sites using HPKP?
I don’t believe that many people are aware of the technology and those who are, might fear bricking their website. It’s not difficult to implement HPKP, but managing the logistics can be. I renew my certificate from Let’s Encrypt by (usually) reusing my key pair so the need for pin rotation will be manageable. For the record, if you’re storing sensitive information on your website then please don’t reuse the CSR.
Recommended reading and sources
Specifications, technical details and tools are available from the following resources:
https://tools.ietf.org/html/rfc7469
https://developer.mozilla.org/
https://scotthelme.co.uk/hpkp-toolset/
https://caniuse.com/#feat=publickeypinning
You done messed up…
In that case, see you in a month.
Alternatively you could head over to slackiuxopmaoigo.onion (Tor).
