Another year of hosting an onion site
The highly anticipated continuation of last year’s riveting tale of fear and loathing on the dark web. I hereby offer a full disclosure of attack patterns observed against my onion and my WordPress installation, respectively.
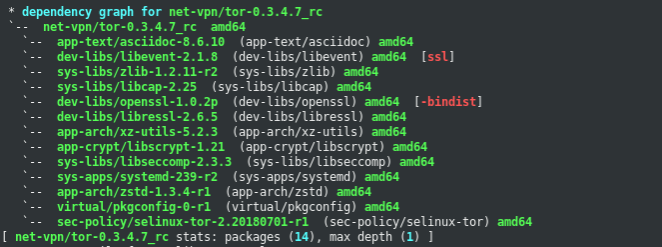
Dependency graph for Tor on Gentoo Linux.
Regarding those attack patterns, well they were clearly so far above my level of expertise that I was unable to identity even a single targeted attack. It was almost like it never happened… scary!
Anyway, unlike the previous year, my onion site now sees substantial traffic. Unfortunately, 95% of the traffic consists of content scrapers, vulnerability scanners and onion spiders. I’ve also been graced by a vast selection of poorly written crawlers that seem incapable of parsing a simple HTML document. Their efforts, however, result in thousands of requests for non-existing resources.
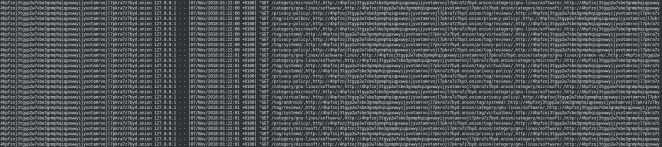
The above mentioned crawlers eventually annoyed me to the extent that I decided to implement a few strict conditions for accessing resources on my onion site. I was so pleased with the result that I later added a modified version for paranoidpenguin.net. Have a look at “Validating HTTP requests using Apache’s THE_REQUEST variable” for the finer details.
Last but not least, I recently launched a new v3 onion that you can read all about at this link if interested. That’s all, hope to see you next year for another exciting report ;-)
