How to enable TLS 1.3 on Gentoo Linux
I figured it was about time for this Gentoo powered blog to enjoy the security and performance enhancements provided by TLSv1.3. However, that meant leaving “Gentoo stable” behind and travel on a journey of discovery into the land of the unmasked and dangerous.
Support for TLSv1.3 was added with OpenSSL 1.1.1, but this version is currently masked on Gentoo. However, the delay appears to be mainly due to incompatible reverse dependencies, and that won’t present much of an issue for my server installation. The only roadblock I’m seeing is MariaDB 10.1 which won’t build with OpenSSL 1.1.1.
MariaDB 10.1 blocking OpenSSL 1.1.1 on Gentoo Linux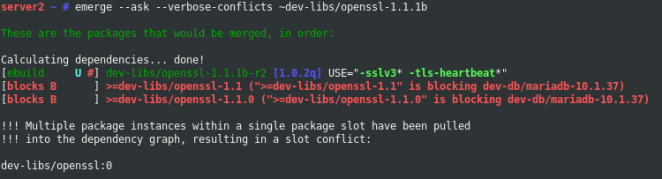
Got HTTP/2 ?
If not, why not have a look at the following article: How to enable HTTP/2 in Apache 2.4 on Gentoo Linux before proceeding. It shouldn’t be horrible outdated (yet).
MariaDB with TLS 1.3 support
MariaDB supports TLSv1.3 since versions 10.2.16 and 10.3.8. I’m going with the 10.3 series, which is the latest stable upstream release. To upgrade to the latest MariaDB 10.3 version, I’ll add the following keyword change to track this release:
echo "=dev-db/mariadb-10.3* ~amd64" >> /etc/portage/package.accept_keywords
Proceed to perform the actual upgrade by issuing:
emerge -av dev-db/mariadb
Upon completion, it’s recommended to execute the MariaDB mysql_upgrade script to check and upgrade the tables to the latest version. Remember to restart the database server after installation before running the upgrade:
rc-service mysql restart mysql_upgrade -u root -p -h localhost
Apache with TLS 1.3 support
Unfortunately, Apache 2.4.34 (Gentoo stable) does not provide TLSv1.3 support so I’ll be moving ahead with Apache 2.4.38 instead. I’ll add the following keyword changes to move to Apache 2.4.38:
echo "~app-admin/apache-tools-2.4.38 ~amd64" >> /etc/portage/package.accept_keywords echo "~www-servers/apache-2.4.38 ~amd64" >> /etc/portage/package.accept_keywords
Proceed to upgrade Apache by issuing:
emerge -av www-servers/apache
OpenSSL 1.1.1
After upgrading MariaDB, I faced no further blocks and could proceed to upgrade OpenSSL to the coveted 1.1.1 release. I’ll add the following keyword change to track the latest available 1.1.1 release:
echo "=dev-libs/openssl-1.1.1* ~amd64" >> /etc/portage/package.accept_keywords
It’s also necessary to unmask OpenSSL 1.1.1 before we’re allowed to install the package. I’ll add the following mask change to allow the installation to move forward:
echo "=dev-libs/openssl-1.1.1*" > /etc/portage/package.unmask/openssl
Proceed to upgrade OpenSSL by issuing:
emerge -av dev-libs/openssl
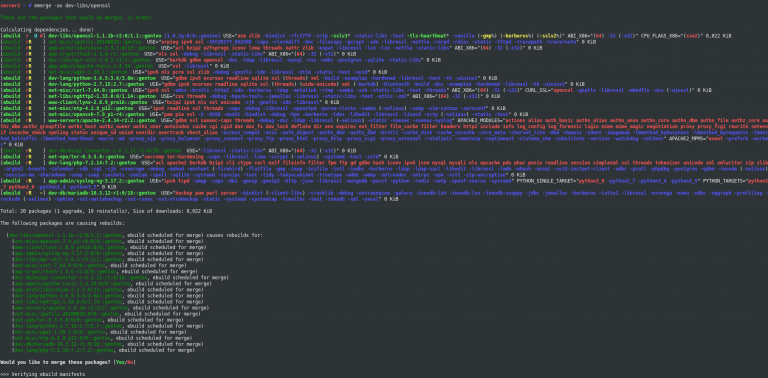
Emerging OpenSSL 1.1.1 on Gentoo Linux.
Depending on your installation it might be necessary to clean up the old library version by issuing:
emerge @preserved-rebuild
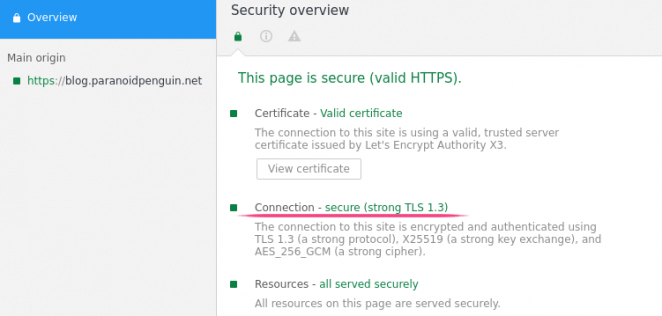
After restarting the relevant services we should see TLSv1.3 encrypted connections filling up the ssl_request_log. All in all, pretty smooth sailing as far as I’m concerned. I’ll report back if things go south.
Even though I didn’t experience any issues, it’s still worth mentioning that having a backup never hurt anyone ;-)